Install mTLS certificates and Test Network
Mutual TLS, or mTLS for short, is a method for mutual authentication. mTLS ensures that the parties at each end of a network connection are who they claim to be by verifying that they both have the correct private key.
TLS
When you visit a website via a secure connection, a digital certificate is sent by the website to your browser. The browser then compares the issuer with a list of already trusted Certificate Authorities (Root CA). In case no match is found, the client browser checks whether a trusted Root CA signs the issuing CA certificate. The browser’s continues verifying the issuer of each certificate until it finds a trusted root or upon reaching the end of the trust chain.
mTLS
In mTLS, different that traditional TLS, both the client and server have a certificate, and both sides authenticate using their public/private key pair, which requires to execute additional steps in order to ensure that both parties are mutually identified.
In a nutshell, the process goes like this:
-
Client connects to server
-
Server presents its TLS certificate
-
Client verifies the server’s certificate
-
Client presents its TLS certificate
-
Server verifies the client’s certificate
-
Server grants access
-
Client and server exchange information over encrypted TLS connection
Why mTLS?
mTLS helps ensure that the communication is secure and trusted between a client and server. This provides an additional layer of security for users who log in to an organization’s network or applications.
This way some types of attacks can be prevented, such as:
-
On-path attacks;
-
Spoofing attacks;
-
Credential stuffing;
-
Brute force attacks;
-
Phishing attacks;
-
Malicious API requests.
How to setup mTLS with a Client in Corda Service?
Once you have your Corda nodes deployed running a CordApp you can download a mTLS Certificate that once its added to your system, will be used for establish the connection between your client and the Corda node.
Instructions
MAC OS
1. Download the mTLS certificate.
2. Open the certificate on Keychain Access (double-click on it), and click on System Keychain:

3. Drag rootCA.crt and keystore.p12 into the My Certificates tab and insert the Keystore password
4. Go to the "Certificates" tab in the Keychain Access window and double-click each uploaded certificate and then open the “Trust” tab and click “Always Trust", close the window by providing the mac user/password.
5. Close the window by providing the Mac user password.

6. MTLS is configured. Restart your browser and open the client URL.
7. Repeat step 5 for rootCA.pem.
8. mTLS is configured. Restart your browser and open the client URL.
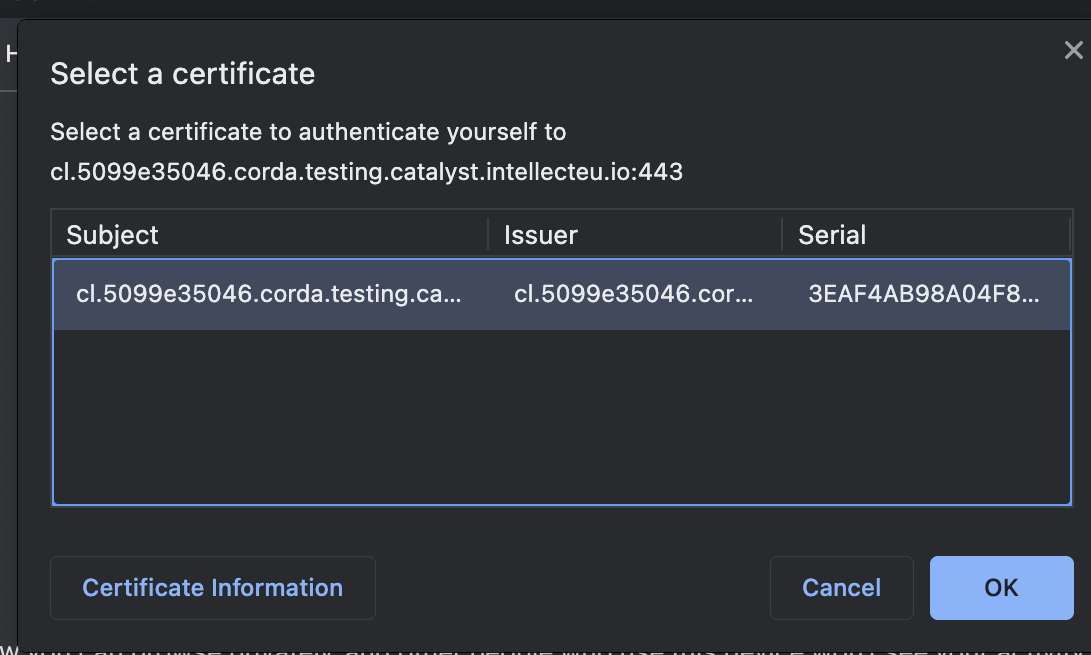
9. Go to the client URL and the browser will request what certificate to use. Select the appropriate certificate and then click OK.